Scams: Recognize the Signs.
go.ncsu.edu/readext?959428
en Español / em Português
El inglés es el idioma de control de esta página. En la medida en que haya algún conflicto entre la traducción al inglés y la traducción, el inglés prevalece.
Al hacer clic en el enlace de traducción se activa un servicio de traducción gratuito para convertir la página al español. Al igual que con cualquier traducción por Internet, la conversión no es sensible al contexto y puede que no traduzca el texto en su significado original. NC State Extension no garantiza la exactitud del texto traducido. Por favor, tenga en cuenta que algunas aplicaciones y/o servicios pueden no funcionar como se espera cuando se traducen.
Português
Inglês é o idioma de controle desta página. Na medida que haja algum conflito entre o texto original em Inglês e a tradução, o Inglês prevalece.
Ao clicar no link de tradução, um serviço gratuito de tradução será ativado para converter a página para o Português. Como em qualquer tradução pela internet, a conversão não é sensivel ao contexto e pode não ocorrer a tradução para o significado orginal. O serviço de Extensão da Carolina do Norte (NC State Extension) não garante a exatidão do texto traduzido. Por favor, observe que algumas funções ou serviços podem não funcionar como esperado após a tradução.
English
English is the controlling language of this page. To the extent there is any conflict between the English text and the translation, English controls.
Clicking on the translation link activates a free translation service to convert the page to Spanish. As with any Internet translation, the conversion is not context-sensitive and may not translate the text to its original meaning. NC State Extension does not guarantee the accuracy of the translated text. Please note that some applications and/or services may not function as expected when translated.
Collapse ▲In our current culture, commerce and conversation often happen over a digital space.
Digital scams come unannounced. But how do you recognize the scam? In this article the tool of good questions will be provided to help give you discernment to recognize scams. Three industry leaders in fraud protection have been referenced for this purpose. The goal is to help build your digital awareness.
Scams may come across multiple digital platforms: a cellular call, a text message, an unopened email or a pop-up message while you are online. Be wary and use these questions to help verify who you’re about to engage with in a digital conversation.
Question 1: How do I verify this person’s identity?
- Phone Call – If you are receiving an unsolicited phone call from someone not in your contact list, thank them for contacting you and say you are not available at this moment. Assure them that you will return the call ASAP. Note their first and last name and ask for their unique identification number (extension, ID, etc.). Hang up. Look online for the accurate number of that organization and use that information to resume the conversation.
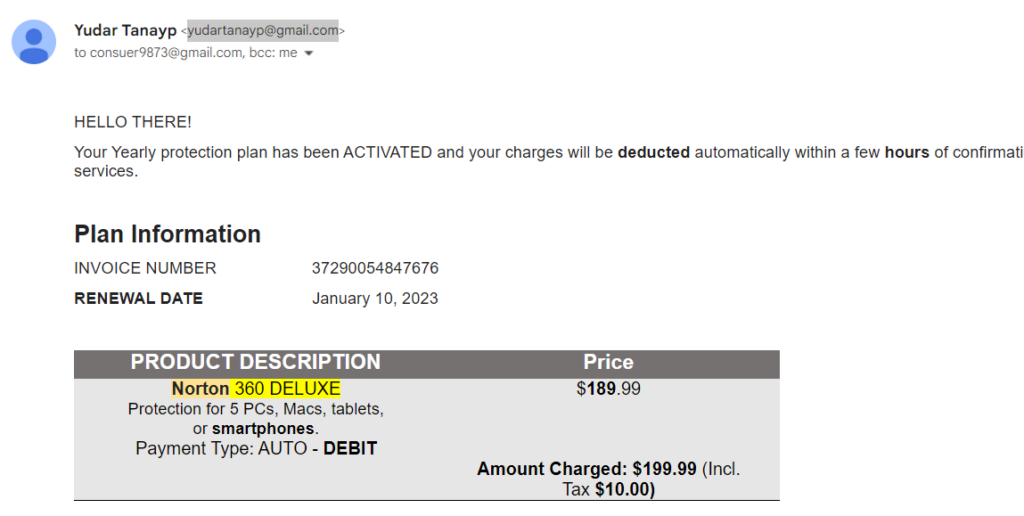
- Email – There are several verification steps to authenticate an email sender. Look at the domain name of the sender. A domain name is like a postal address. It’s difficult to spoof because it is routed by a thirdparty. Use the screenshot to compare/contrast how to verify the sender’s domain. The below message from The Washington Post is legitimate because its domain is washingtonpost.com while the message from Norton Antivirus is a scam because its domain is a Gmail address.
- Text/SMS – If the sender is not in your contact list, beware. Do not click on any links in the text. Ask yourself, did I sign up for this notification? For instance, if you requested your dentist to send you appointment reminders, then verify that the number matches one you have in your contacts for that provider. It is the providers’ responsibility to identify themselves to you and you have the right to ignore their text if that is not clear.
- Pop-Up – Notifications that appear on your desktop while surfing on the internet are generally not trustworthy. Most browsers will automatically block them. If your website requires them you can make an exception for that domain.
Question 2: How to make my internet browsing experience safer?
Depending on your browser there are enhanced features to protect your online data and identity. Below are two links for activating those safety features.
- Google Chrome link on how-to activate that feature.
- Microsoft Edge link on how-to activate that feature.
If you are online in a public/open domain such as at a coffee shop, do not exchange personal information. Save any digital activity that involves financial transactions or other sensitive data for a time when you are on a secure network.
Question 3: How else might I recognize a scammer?
The Federal Trade Commission article provides details for each of these spam characteristics is worth the read. One strength of this FTC article is that it helps you become aware of the digital language. Below is an excerpt:
- Scammers say there’s a Problem or a Prize. Both options are extreme. One is meant to scare you and the second is offering something for nothing.
- Scammers Pressure you to act immediately. Take your time to verify their story with a third party.
- Scammers tell you to Pay in a specific way.
Being digital literate means understanding the terminology/ the words used in the digital marketplace.
The FTC has a list of common scams, recognizing them helps prevent your chances of becoming a victim. The Consumer Financial Protection Bureau also has a brief list of a few common terms to know for safe digital navigation. If you want a full digital dictionary use this resource. The dictionary author, SEON, is a business dedicated to fraud prevention. If you have an email address that seems suspicious you can use their online tool to help diagnose the risk.
The FTC offers a sound piece of advice when navigating potential scams: “Stop and talk to someone you trust. Before you do anything else, tell someone — a friend, a family member, a neighbor — what happened. Talking about it could help you realize it’s a scam.” Scams are intended to provoke your emotions and lead you to make quick decisions. Make time to think and invite a trusted friend into that space. Everyone has been a target of scams at some point in their life. It’s nothing to fear, but it is something to learn about and even to learn from.
Citations:
If you have any questions please contact Jeffrey Cates, Extension Agent – Digital Literacy, 336-641-2400, jeff_cates@ncsu.edu.